Cloud security assessments evaluate an organisation’s cloud infrastructure to identify vulnerabilities, misconfigurations, and risks. These assessments ensure robust protection for data and applications in dynamic cloud environments.
A cloud security assessment systematically reviews cloud setups, including access controls, encryption, and network configurations. It promotes shared responsibility between users and providers like AWS or Azure, uncovering hidden threats before exploitation.
The process involves scoping the environment, gathering data on configurations and policies, analysing risks, and testing via scans or penetration simulations. Key components cover identity management, storage security, workload protection, and incident response readiness.
These assessments strengthen overall security posture, detect attack vectors in APIs or containers, and prioritise fixes for high-impact assets. They reveal compliance gaps and enable proactive defences against evolving threats, such as unauthorised access and data breaches.
Cloud environments expand rapidly, often introducing shadow IT or misconfigurations that attackers target. Regular assessments are essential for regulatory compliance (e.g., GDPR, ISO 27001), risk mitigation, and proving security to stakeholders in regulated sectors.
Why Cloud Security Assessments / Benefits
- Protection of Sensitive Data: Conducting a cloud security assessment is essential to safeguard sensitive data stored and processed in cloud environments. Assessments help identify vulnerabilities and weaknesses in cloud infrastructure, applications, and configurations that could potentially expose sensitive information to unauthorised access or breaches.
- Compliance with Regulations: A thorough cloud security assessment helps organisations comply with relevant regulations, such as the Payment Card Industry Data Security Standard (PCI DSS), reducing the risk of non-compliance penalties and legal liabilities.
- Mitigation of Security Risks: Cloud environments are susceptible to various security threats, including data breaches, malware attacks, and insider threats. By conducting regular security assessments, organisations can proactively identify and address security risks before they escalate into serious incidents, minimising the likelihood of data breaches and business disruptions.
- Assurance of Data Integrity and Availability: Ensuring the integrity and availability of data stored in the cloud is critical for business continuity and maintaining customer trust. Cloud security assessments help organisations verify the reliability of cloud service providers’ infrastructure, data replication processes, and disaster recovery plans, ensuring data integrity and availability in the event of hardware failures or natural disasters.
- Strengthening of Security Posture: Continuous evaluation and improvement of cloud security measures are vital to adapt to evolving cyber threats and vulnerabilities. Cloud security assessments provide valuable insights into the effectiveness of existing security controls and enable organisations to implement additional measures to strengthen their security posture and resilience against emerging threats.
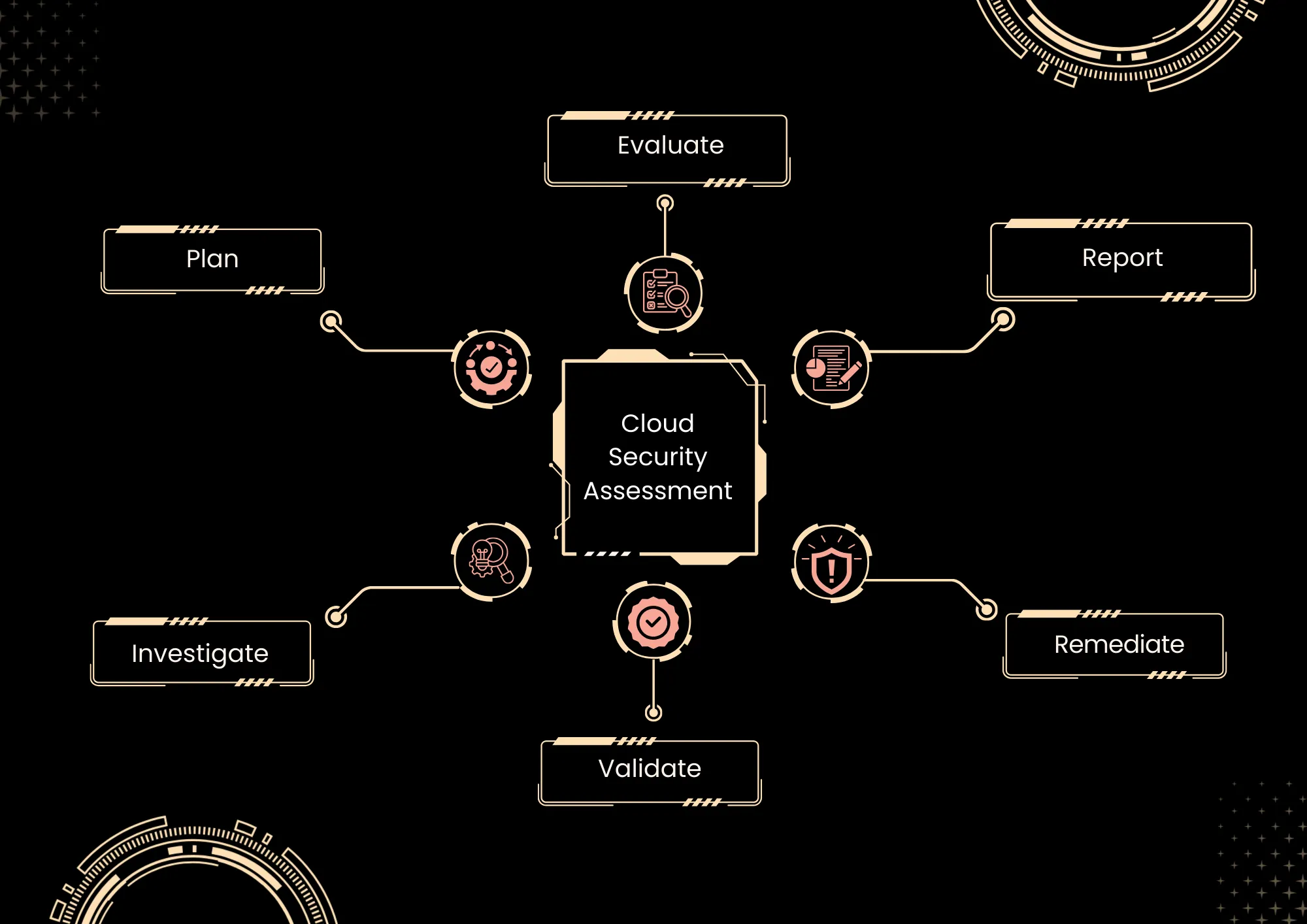
Cyberverse Approach
At Cyberverse, we go beyond basic cloud audits. Our cloud security assessments provide comprehensive visibility into your cloud infrastructure, ensuring your security posture aligns with best practices, compliance frameworks, and business objectives.
By identifying vulnerabilities and weaknesses, and providing actionable remediation strategies, we help organisations proactively reduce risk and maintain a secure, well-governed cloud environment.
- Initial Assessment and Scoping
- Risk Identification and Analysis
- Compliance Evaluation
- Security Control Assessment
- Reporting and Recommendations
- Technical Report and Roadmap
- Alignment with Government & Industry Frameworks and Regulations
Frameworks we cover
- CSA STAR
- CSA Cloud Controls Matrix
- NIST Cybersecurity Framework
- SOC 2


