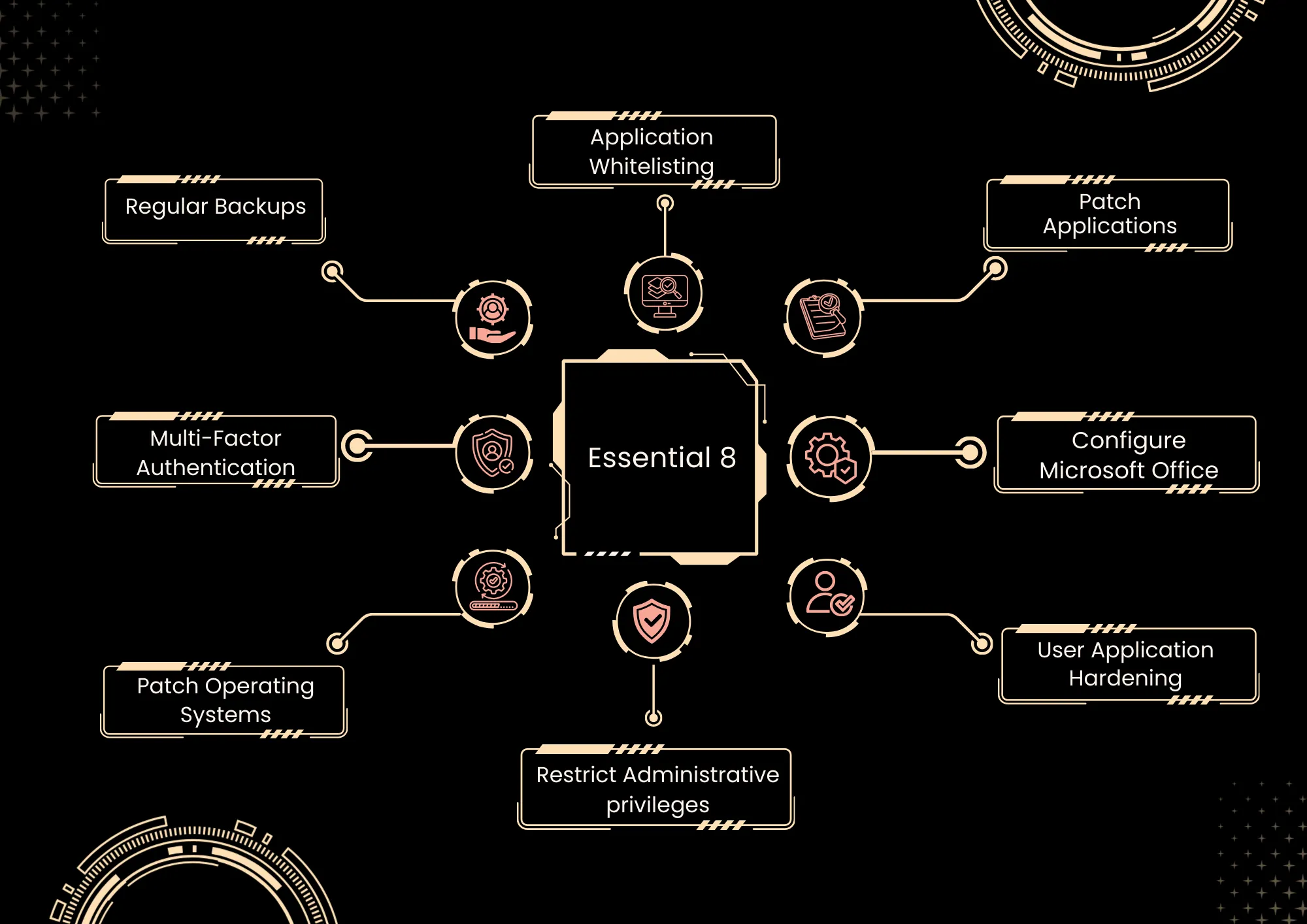
The Essential 8 principles are developed by the Australian Cyber Security Centre (ACSC), which operates under the Australian Signals Directorate (ASD) and the Australian Federal Government. These eight controls have been derived from hundreds of sources and adapted into a foundational framework for all organisations.
The Essential Eight assesses how well your organisation's security controls perform against the Essential Eight Framework, eight vital cybersecurity strategies that account for 85% of cyber threats.
Why Essential 8 / Benefits
- Improve your organisation’s cyber security: Essential 8 provides organisations with a targeted approach to defending against the most prevalent cyber threats. The controls concentrate on safeguarding the areas of businesses most frequently targeted and on reducing the consequences of successful attacks. Adherence to these principles can significantly enhance your cybersecurity defences. Increase your business opportunities.
- Maturity levels to fit any-sized organisation: A three-stage maturity level is attached to each control to help organisations correctly size their implementation based on their risk appetite. It means you can enhance your cybersecurity incrementally.
- Determination of the cyber posture's maturity level: The Essential Eight Maturity Model (Levels 0–3) enables organisations to objectively assess how well each control (e.g., MFA, backups, patching) is implemented. This provides a clear picture of overall cyber posture, highlights gaps, and gives executives an easy‑to‑understand benchmark for uplift roadmaps.
- Reduces financial and reputational damages: By focusing on high-value controls that prevent or mitigate common threats, such as ransomware, the Essential Eight framework reduces the likelihood and severity of costly incidents. Robust controls for patch management, data backups, and administrative restrictions directly reduce recovery costs, operational downtime, and reputational damage from data breaches.
- Essential 8 policy coverage across the environment: The essential Eight facilitates the development of aligned policies and standards, such as application control, operating system patching, Service Level Agreements (SLAs), and Multi-Factor Authentication (MFA) requirements, which are uniformly applied to endpoints, servers, and cloud workloads. Associating policies with each mitigation strategy ensures comprehensive coverage across various business units, third-party entities, and remote users, thereby minimising vulnerabilities.
- Continuous monitoring of the environment against the framework: Logging, configuration management, and vulnerability scanning are employed to continuously monitor compliance with each Essential Eight requirement (e.g., patch timeframes, MFA scope). Dashboards and periodic reassessments against the maturity model facilitate ongoing enhancement rather than one-off audits.
- Mitigates common cyber threats and protects sensitive data: The controls are explicitly selected to counter prevalent techniques, including phishing‑delivered malware, exploitation of unpatched systems, and credential theft. When implemented at higher maturity levels, the Essential Eight significantly improves protection of sensitive and regulated data by limiting attacker paths to compromise and exfiltrate data.
- Provides a structured approach: The Essential Eight presents a prioritised, prescriptive set of eight strategies rather than an exhaustive list of generic controls. The integration of explicit mitigation strategies, well-defined outcomes, and maturity criteria provides a structured roadmap for planning, budgeting, and monitoring cybersecurity improvements.
Cyberverse Approach
We implement a risk-based, business-aligned methodology for the Essential Eight. Our services go beyond the mere assessment of technical controls; we support their integration and operationalisation within your environment, offering pragmatic strategies to achieve and maintain your targeted maturity level.
Whether starting at the foundational level or targeting Maturity Level 3, we collaborate closely with your team to ensure your E8 program is both effective and sustainable.
- Understand your ‘Why’?
- Scoping the Essential 8 boundaries & Maturity Level
- Essential 8 Assessment & Recommendations
- Technical Report
- Advisory Support with Essential 8 Implementation
- Training & Awareness Programs
- Ongoing Monitoring & Review
- Tailored Uplift Roadmaps
- Alignment with Government & Industry Expectations


